
Such as the phpssh2.h header file. 9) replace the old version of ssh2.c with the new version of ssh2.c (and any other files you downloaded). 10) From the terminal: cd to the source directory (for me ssh2-0.9/ssh2-0.9/). (Continued in a PART 2 comment). Once you select a location for the key, you'll be prompted to enter an optional passphrase which encrypts the private key file on disk. If you enter one, you will have to provide it every time you use this key (unless you are running SSH agent software that stores the decrypted key).
The program SSH (Secure Shell) provides an encrypted channel for logging into another computer over a network, executing commands on a remote computer, and moving files from one computer to another. SSH provides strong host-to-host and user authentication as well as secure encrypted communications over the internet.
If you aren't sure which site to use, you can enter your product key using the. Office 2011 product key free. If your product key is valid, the Virtual support agent provides a link to download Office.
SSH2 is a more secure, efficient, and portable version of SSH that includes SFTP, which is functionally similar to FTP, but is SSH2 encrypted. AtIndiana University, UITS has upgraded its central systemsto SSH2 (usually the OpenSSH version), and encourages those concernedwith secure communications to connect using an SSH2client.

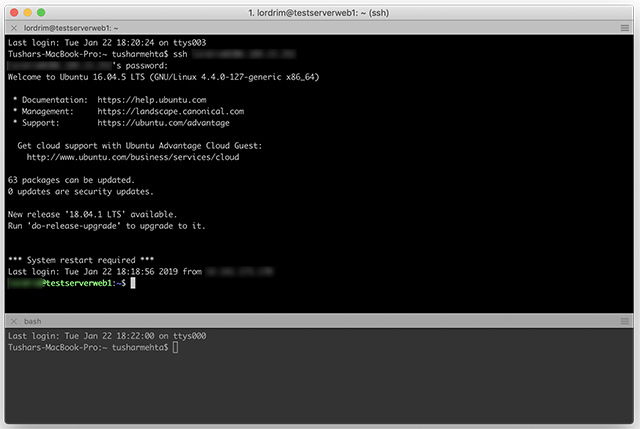
macOS comes with OpenSSH built in. For Windows, you will have to download a third-party SSH client.
When connecting to a server for the first time, SSH presents you with a host key fingerprint for that server and asks you to confirm you wish to save the new host key to the local database. Before agreeing, you should compare this fingerprint with one you obtain by some other means (for example, by telephone) from the server administrators to avoid connecting to an imposter server. To avoid this message the next time you connect, click Yes. Video copilot element 3d v2 crack mac.
Ssh2 For Mac Os
Rather than validating identities via passwords, SSH2 can also use public key encryption to authenticate remote hosts. For example, if you were to connect to a remote host called global.conspiracy.org (also running SSH2), SSH2 would use this system to verify that this remote system is authentic. If you wish, you can set up SSH2 to use public key authentication rather than passwords for logging into your other accounts, much like the Unixrlogin program. Forinstructions, see Set up SSH public-key authentication to connect to a remote system.
Ssh2 Mac Terminal

Such as the phpssh2.h header file. 9) replace the old version of ssh2.c with the new version of ssh2.c (and any other files you downloaded). 10) From the terminal: cd to the source directory (for me ssh2-0.9/ssh2-0.9/). (Continued in a PART 2 comment). Once you select a location for the key, you'll be prompted to enter an optional passphrase which encrypts the private key file on disk. If you enter one, you will have to provide it every time you use this key (unless you are running SSH agent software that stores the decrypted key).
The program SSH (Secure Shell) provides an encrypted channel for logging into another computer over a network, executing commands on a remote computer, and moving files from one computer to another. SSH provides strong host-to-host and user authentication as well as secure encrypted communications over the internet.
If you aren't sure which site to use, you can enter your product key using the. Office 2011 product key free. If your product key is valid, the Virtual support agent provides a link to download Office.
SSH2 is a more secure, efficient, and portable version of SSH that includes SFTP, which is functionally similar to FTP, but is SSH2 encrypted. AtIndiana University, UITS has upgraded its central systemsto SSH2 (usually the OpenSSH version), and encourages those concernedwith secure communications to connect using an SSH2client.
macOS comes with OpenSSH built in. For Windows, you will have to download a third-party SSH client.
When connecting to a server for the first time, SSH presents you with a host key fingerprint for that server and asks you to confirm you wish to save the new host key to the local database. Before agreeing, you should compare this fingerprint with one you obtain by some other means (for example, by telephone) from the server administrators to avoid connecting to an imposter server. To avoid this message the next time you connect, click Yes. Video copilot element 3d v2 crack mac.
Ssh2 For Mac Os
Rather than validating identities via passwords, SSH2 can also use public key encryption to authenticate remote hosts. For example, if you were to connect to a remote host called global.conspiracy.org (also running SSH2), SSH2 would use this system to verify that this remote system is authentic. If you wish, you can set up SSH2 to use public key authentication rather than passwords for logging into your other accounts, much like the Unixrlogin program. Forinstructions, see Set up SSH public-key authentication to connect to a remote system.
Ssh2 Mac Terminal
Ssh2 Mac Spec
For more, see: Dlna mac os x.
Ssh2 Mac
- Using SSH from the University Information Security Office (UISO) at IU
